ADMIN-ELECTRIK_CAT
Administrator
 Din: CAT LAND
Inregistrat: acum 19 ani
Postari: 8870
|
|
Malware Overview
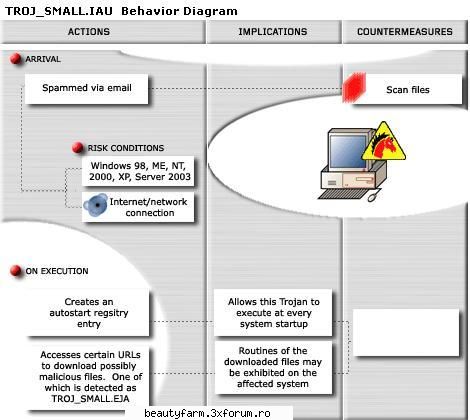
This Trojan usually arrives on a system as an attachment to spammed email messages.
Upon execution, it drops a copy of itself as ISXA.EXE in the Windows system folder. It also drops a non-malicious text file named C656.TX in the %System%Drivers folder. The said text file contains several URLs.
(Note: %System% is the Windows system folder, which is usually C:WindowsSystem on Windows 98 and ME, C:WINNTSystem32 on Windows NT and 2000, or C:WindowsSystem32 on Windows XP and Server 2003.)
It connects to the said URLs to download certain files. As a result of this download routine, the behavior of the said files can be observed on the affected system. Trend Micro detects one of the downloaded files as TROJ_SMALL.EJA.
Descrizione creata: 2007-03-07
Soluzione:
Terminating the Malware Program
This procedure terminates the running malware process.
Open Windows Task Manager.
• On Windows 98 and ME, press
CTRL+ALT+DELETE
• On Windows NT, 2000, XP, and Server 2003, press
CTRL+SHIFT+ESC, then click the Processes tab.
In the list of running programs*, locate the process:
ISXA.EXE
Select the malware process, then press either the End Task or the End Process button, depending on the version of Windows on your computer.
To check if the malware process has been terminated, close Task Manager, and then open it again.
Close Task Manager.
--------------------------------------------------------------------------------
*NOTE: On computers running Windows 98 and ME, Windows Task Manager may not show certain processes. You can use a third party process viewer such as Process Explorer to terminate the malware process.
On computers running all Windows platforms, if the process you are looking for is not in the list displayed by Task Manager or Process Explorer, continue with the next solution procedure, noting additional instructions. If the malware process is in the list displayed by either Task Manager or Process Explorer, but you are unable to terminate it, restart your computer in safe mode.
Editing the Registry
This malware modifies the computer's registry. Users affected by this malware may need to modify or delete specific registry keys or entries. For detailed information regarding registry editing, please refer to the following articles from Microsoft:
HOW TO: Backup, Edit, and Restore the Registry in Windows 95, Windows 98, and Windows ME
HOW TO: Backup, Edit, and Restore the Registry in Windows NT 4.0
HOW TO: Backup, Edit, and Restore the Registry in Windows 2000
HOW TO: Back Up, Edit, and Restore the Registry in Windows XP and Server 2003
Removing Autostart Entry from the Registry
Removing autostart entries from the registry prevents the malware from executing at startup.
If the registry entry below is not found, the malware may not have executed as of detection. If so, proceed to the succeeding solution set.
Open Registry Editor. Click Start>Run, type REGEDIT, then press Enter.
In the left panel, double-click the following:
HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>
Windows>CurrentVersion>Run
In the right panel, locate and delete the entry:
Isxa = "isxa.exe"
Removing Malware Entry from the Registry
Still in the Registry Editor, in the left panel, double-click the following:
HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>
Windows>CurrentVersion
In the right panel, locate and delete the entry:
Xcq = "{Random numbers}"
Close Registry Editor.
Deleting the Malware File(s)
Right-click Start then click Search... or Find..., depending on the version of Windows you are running.
In the Named input box, type:
c656.tx
In the Look In drop-down list, select My Computer, then press Enter.
Once located, select the file then press SHIFT+DELETE.
Important Windows ME/XP Cleaning Instructions
Users running Windows ME and XP must disable System Restore to allow full scanning of infected computers.
38.2KB
_______________________________________
 PM-URI PM-URI  №1 №1
  TUTORIAL 3XFORUM TUTORIAL 3XFORUM
 | REPORT BROKEN LINKS | | REPORT BROKEN LINKS | 
|
|


 №1
№1